Know How To Fix Mrt.Exe From Pc
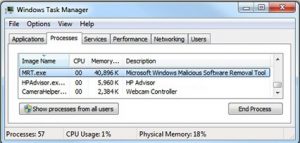
mrt.exe is a Windows executable file developed by Microsoft. The main function of these executable files is to run the removal tool from Microsoft.
mrt.exe is a trusted software that is approved by Microsoft.
This desktop application helps you to prevent your system against several types of malicious infections.
It is compatible with the Windows operating system.
However, malware writers use original file names, distribution agents or malware. Usually, locate your infectious files to another location instead of C: / Windows / System32 folder.
This propagation hides the Trojan virus. It is completely Call assault system performance and cause discomfort.
mrt.exe could be used to load infectious files in the registry and cause hassles. Even change the system files, the startup to automatically start the malicious process.
There is a change in the system configuration and allow another vulnerable threat to enter. It will open back door and will enable another virus to enter easily.
Actually one of the unsafe programs that make annoying changes. It only develops to make an income. Therefore, it is suggested that you look for a practical solution and delete mrt.exe.
Table of Contents
What is Mrt.Exe?
mrt.exe is a legitimate file that uses the Windows operating system to ensure that some specific programs run correctly.
However, many of the cyber criminals make use of this file name to circulate their own infectious files that once installed on a computer is started and replace the original one that causes the system to throw mrt.exe errors on the screen.
If such conditions happen with your computer, you would immediately notice the problem of system instability and the PC starts to freeze and hang up regularly.
This dangerous process elevates other processes to obtain administration rights and will begin to control the infected PC.
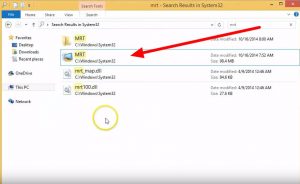
The storage location of mrt.exe changes depending on the version used of the operating system. Most likely, this file is located in the c: \ windows \ system32 or c: \ Winnt \ System32 directories.
In some cases, it is stored in the dllcache directory if it is present on your PC. Since the name of the process looks very genuine; therefore, it easily manages to disguise itself.
How does the mrt.exe error work?
The mrt.exe infections install their executable on the marked PC in a very secret way. They copy their payloads in Windows system folders and alter records simultaneously so that this file runs automatically every time the system is started.
mrt.exe will modify the subkey named HKEY_LOCAL_MACHINE \ Software \ Microsoft \ Windows \ CurrentVersion \ Run so that it starts at the start of the PC.
Once it settles, it also connects the workstation with a remote host to perform unpleasant tasks such as:
- to download arbitrary harmful files in the back door
- receive coded instructions from your developer
- to get the secret configuration
- to transfer cheated data on the infected PC to the remote server
Some common error messages
- First one “Mrt.exe application error.”
- The second one “Mrt.exe is not a valid Win32 application.”
- The third one “Mrt.exe. “This program does not respond.”
- Fourth one “Error when starting the program: mrt.exe.”
- Fifth one “Application path error: mrt.exe.”
- Finally, “Mrt.exe failed.”
How is mrt.exe put inside the PC?
Cybercriminals use multiple means to circulate mrt.exe on the target PC. It could come through hyperlinks from malicious websites, grouping, social engineering spam, peer-to-peer file-sharing networks, email attachments and so on.
It has the ability to exploit your PC security vulnerabilities and is installed in secret without your knowledge. Another easy way is to attach the payload with spam email campaigns and cyber-crooks doing this a lot.
Such spam emails are very cleverly designed with header information forged giving an impression that the mail comes from some government organization, shipping company and so on.
Usually, these emails have many grammatical and spelling errors.
At some point, cyber-criminals also promote mrt.exe as useful software or a necessary Windows system file. For example, you may notice a false message asking you to update Java or Adobe Flash Player files and so on.
Problems and damages caused by mrt.exe
First of all, understand that mrt.exe is not an independent infection and, instead, it is bound to bring so many other viral infections by exploiting security loopholes.
Therefore, you will face several performance problems online, as well as offline simultaneously and commit to the security of personal data as well. Some of the common issues that can be noticed are:
- Displays fake alerts that say your PC is infected with malware
- Ask victims to click on unpleasant notification hyperlinks to solve problems
- Redirects the website about sponsored dangerous websites
- Blocks access to several legitimate programs
- Automatically deactivates important processes and records
Most dll files are useful and are responsible for executing predefined functions without problems.
However, there are malicious programs including malware and browser hijackers that are formed by dll files like mrt.exe and alter important PC settings unnecessarily.
They even allow cyber-criminals to access their workstation.
How to manually remove it
- Open the command prompt window: Press the “Start” button in the taskbar and go to “Run” to start the “Run” tool. Write the “cmd” command on it and press the “OK” button.
- Locate dll files: once the command prompt window opens, you have to locate the exact path as mentioned in the screenshot below. Type “CD” to change the current directory, press the Space button, enter the path of the dlll file, and then press Enter. Use the “dir” command if you want to display the content on the screen.
- Unregister the unwanted dll: after locating the directory from which you want to uninstall the dll file, type “regsvr32 / u [DLL_NAME]” and click on the Enter button.
- Cancel the registration successfully: once the targeted dll files are deregistered, a conformation message appears on the screen.
The steps mentioned above can fix mrt.exe, but there is always a chance that you will not detect it on your own, as it is very misleading.
The process is cumbersome and requires a lot of precision and experience. Therefore, it is always better to use a powerful anti-malware tool, especially for the novice user.


[…] 1: Open the “Regedit” with just typing in the execution dialog box. Please wait a few seconds to open […]